Compliance is not paperwork. It is protection, trust and business continuity.
Assessment + Evidence = Credible governance
When you can demonstrate periodic controls, tracked remediation and measurable risk reduction,
your organization is stronger with customers, partners, investors and auditors.
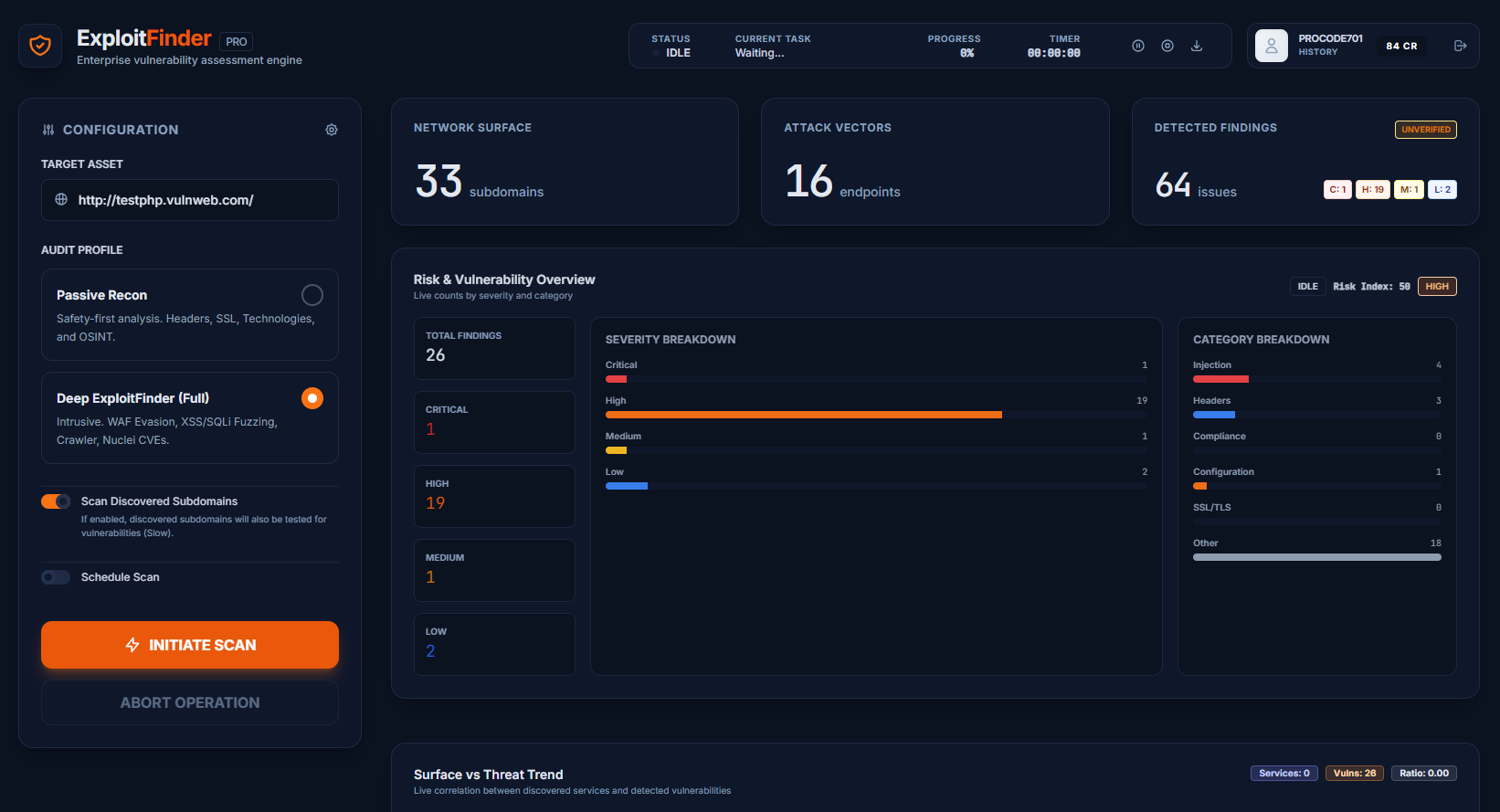
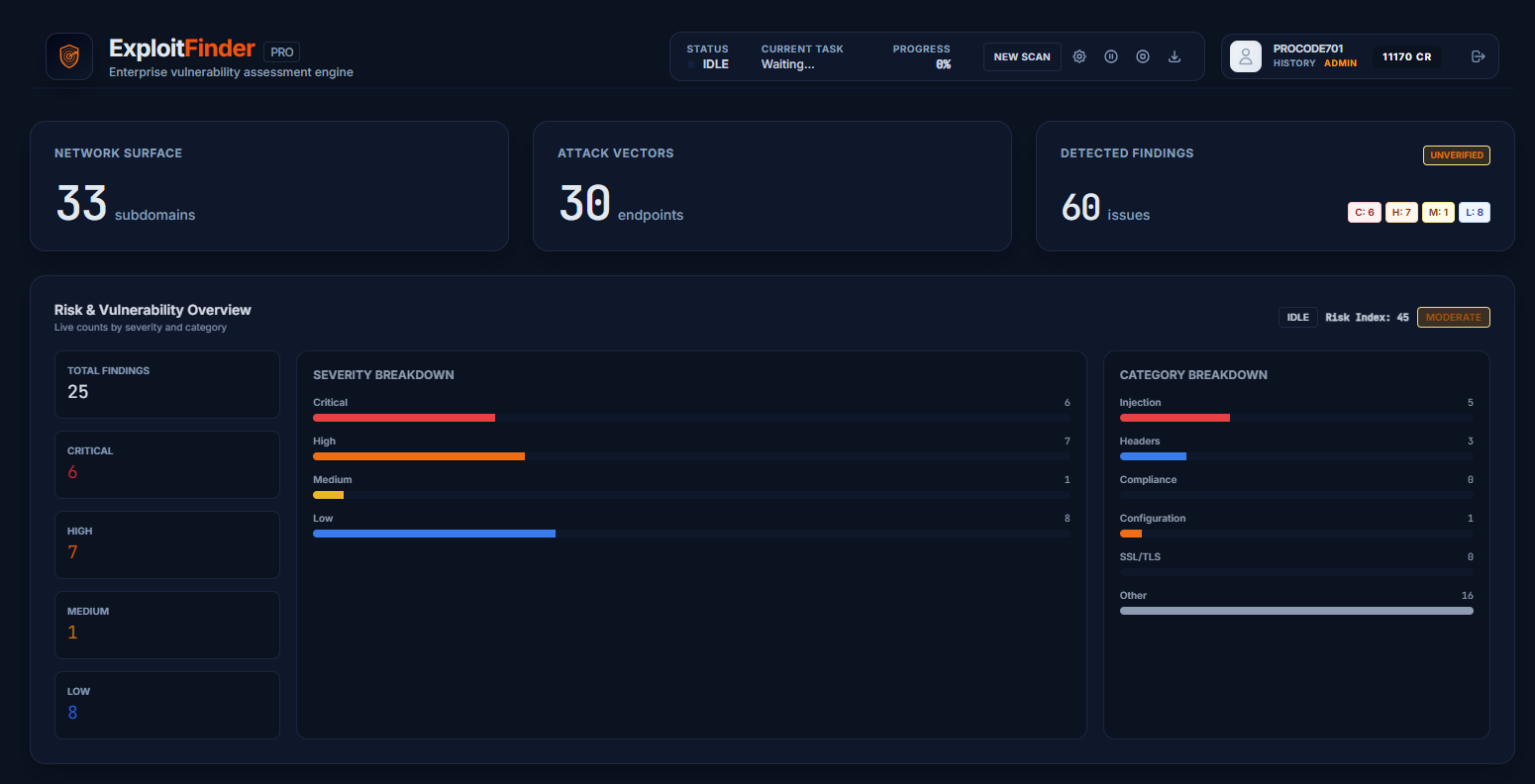
Exploit Finder reports help build evidence for audit and compliance workflows,
reducing operational and reputational exposure.
- ISO 27001 / ISMS readiness
- SOC 2 control evidence support
- NIST-aligned vulnerability management
- OWASP best-practice verification
- Documentation support for NIS2/GDPR accountability processes
- Ready output for enterprise client and vendor assessments
Talk to an advisor